Archive for the ‘security’ category: Page 108
Oct 17, 2017
China to build giant facial recognition database to identify any citizen within seconds
Posted by Derick Lee in categories: robotics/AI, security
However, some researchers said it was unclear when the system would be completed, as the development was encountering many difficulties due to the technical limits of facial recognition technology and the large population base.
Project aims to achieve an accuracy rate of 90 per cent but faces formidable technological hurdles and concerns about security.
PUBLISHED : Thursday, 12 October, 2017, 9:01pm.
Oct 7, 2017
Using Behavioral Biometrics for Wearable Glasses
Posted by Shailesh Prasad in categories: privacy, security, wearables
Through behavioral biometrics, a wearable glasses continuous authentication system improves privacy protection by detecting imposters through voice & touch.
Oct 6, 2017
This startup says its 3D face authentication will work on all kinds of smartphones
Posted by Shailesh Prasad in categories: mobile phones, security
Most of us aren’t going to shell out for an iPhone X, but we can still log in with our faces.
Oct 3, 2017
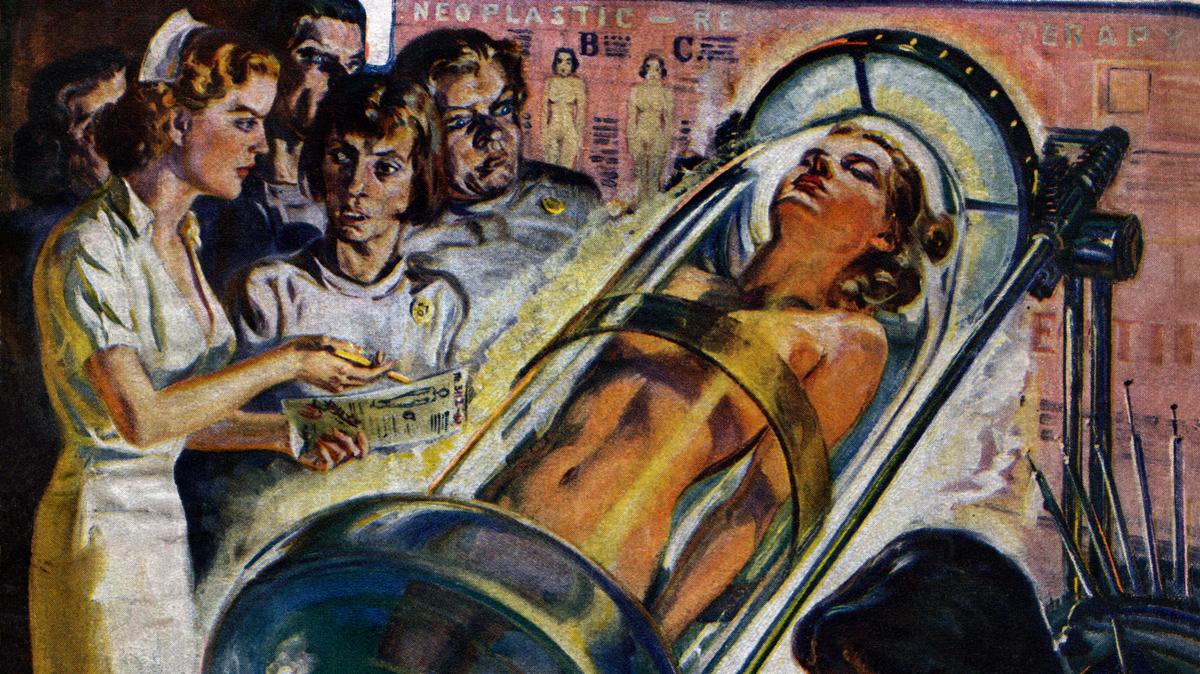
To Combat Radical Violence in America, We Need Radical Medicine
Posted by Zoltan Istvan in categories: biotech/medical, drones, government, neuroscience, security, terrorism
With yesterday’s terrible shooting tragedy, I’m hearing lots of calls for more gun control to reduce violence in the US. But that’s essentially impossible to accomplish. There are 300 million guns in America. Congress faces a statistical impossibility to make a real dent in gun control and possession (politicians saying otherwise are playing you for votes—the gov is not going to go house to house to collect guns). HOWEVER, better ways to combat terrorism and gun violence could be achieved through better medicine and figuring out better ways to keep wounded peope alive. We should focus our energy and science money on treating trauma victims (and also on prevention of mental disease and sociopaths). Also, drones can be designed to seek out shooters in public places in 30 seconds and stop what they’re doing (instead of letting them shoot for 10 minutes). Why don’t major public venues and events have them yet? Ask you government? Demand better responses so our society is safer. Also, entreprenuers, get out there and do something about this. Hotels would pay big money for see-through-wall technology that would alert staff that someone has 20 weapons in a room. Lots of this tech is already here. All these terrorism and gun violence issues can be best figured out by tech and science. Stop sending prayers, and instead send some engineers and technologists to solve the problems. This tragic ongoing violence will continue until tech and science solves it.
“If you make the human body virtually indestructible, being wounded loses some of its relevance.”
America is reeling in shock from multiple shooting tragedies. The national feeling is that the violence is increasing in frequency and there’s no end to the angst.
Continue reading “To Combat Radical Violence in America, We Need Radical Medicine” »
Sep 30, 2017
A Smartphone Made in Russia Claims to be “Surveillance-Proof”
Posted by Shailesh Prasad in categories: mobile phones, security, surveillance
Russian IT security firm InfoWatch designed the phone for the corporate market, and claims users will control all information that passes through it.
Sep 30, 2017
Apple just released new information about how facial recognition on the iPhone X works
Posted by Shailesh Prasad in categories: mobile phones, robotics/AI, security
Apple updated the security and privacy information on its website on Wednesday, revealing new details about how its new facial-recognition technology works.
The new details come about a month before Apple’s most advanced iPhone, the iPhone X, goes on sale. The banner feature of the iPhone X is a facial-recognition tool called Face ID that unlocks the phone, replacing the fingerprint sensor.
Since Face ID and its corresponding 3D camera, called TrueDepth, were announced earlier this month, the technology has attracted a lot of attention and speculation from privacy advocates and security experts. Sen. Al Franken even wrote an open letter to Apple CEO Tim Cook with 10 questions about the technology.
Sep 29, 2017
Facing poverty, academics turn to sex work and sleeping in cars
Posted by Derick Lee in categories: health, security, sex
Adjuncting has grown as funding for public universities has fallen by more than a quarter between 1990 and 2009. Private institutions also recognize the allure of part-time professors: generally they are cheaper than full-time staff, don’t receive benefits or support for their personal research, and their hours can be carefully limited so they do not teach enough to qualify for health insurance.
Adjunct professors in America face low pay and long hours without the security of full-time faculty. Some, on the brink of homelessness, take desperate measures.
Sep 23, 2017
Malicious code written into DNA infects the computer that reads it
Posted by Klaus Baldauf in categories: biotech/medical, computing, security
In a mind-boggling world first, a team of biologists and security researchers have successfully infected a computer with a malicious program coded into a strand of DNA.
It sounds like science fiction, but I assure you it’s quite real — although you probably don’t have to worry about this particular threat vector any time soon. That said, the possibilities suggested by this project are equally fascinating and terrifying to contemplate.
The multidisciplinary team at the University of Washington isn’t out to make outlandish headlines, although it’s certainly done that. They were concerned that the security infrastructure around DNA transcription and analysis was inadequate, having found elementary vulnerabilities in open-source software used in labs around the world. Given the nature of the data usually being handled, this could be a serious problem going forward.
Continue reading “Malicious code written into DNA infects the computer that reads it” »
Sep 19, 2017
Someone checked and, yup, you can still hijack Gmail, Bitcoin wallets etc via dirty SS7 tricks
Posted by John Gallagher in categories: bitcoin, security
Two-factor authentication by SMS? More like SOS
Once again, it’s been demonstrated that vulnerabilities in cellphone networks can be exploited to intercept one-time two-factor authentication tokens in text messages.