PLUS: MGM settles breach suits; AWS doesn’t trust you with security defaults; A new. NET backdoor; and more.


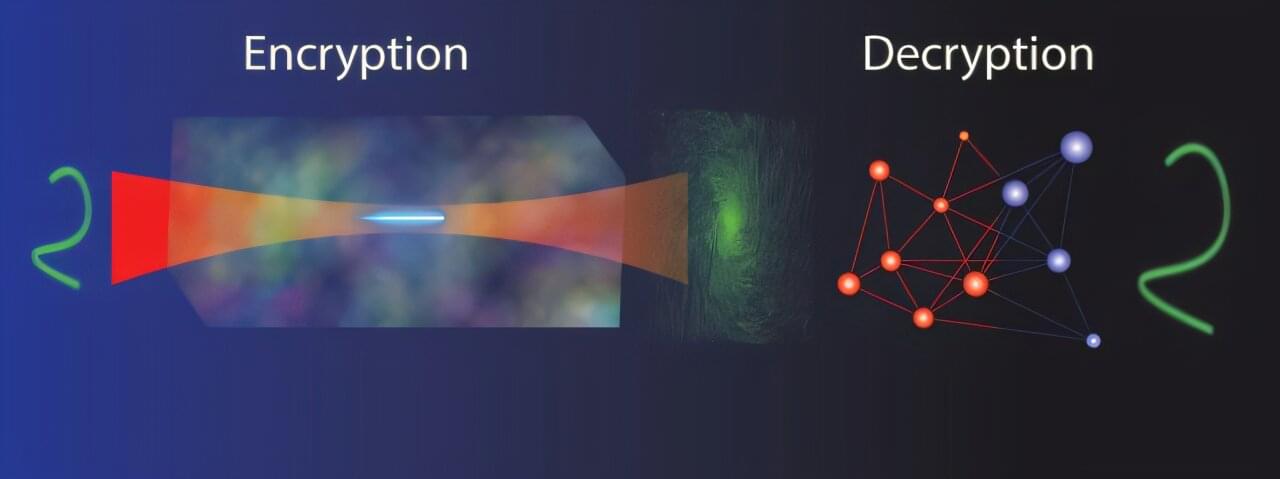
As the demand for digital security grows, researchers have developed a new optical system that uses holograms to encode information, creating a level of encryption that traditional methods cannot penetrate. This advance could pave the way for more secure communication channels, helping to protect sensitive data.
“From rapidly evolving digital currencies to governance, health care, communications and social networks, the demand for robust protection systems to combat digital fraud continues to grow,” said research team leader Stelios Tzortzakis from the Institute of Electronic Structure and Laser, Foundation for Research and Technology Hellas and the University of Crete, both in Greece.
“Our new system achieves an exceptional level of encryption by utilizing a neural network to generate the decryption key, which can only be created by the owner of the encryption system.”
In today’s AI news, ElevenLabs said on Thursday it has raised $180 million in a new funding round that triples the voice cloning artificial intelligence startup’s valuation to $3.3 billion. The Series C funding round was co-led by Andreessen Horowitz and Iconiq Growth, with participation from additional new investors.
On Thursday, OpenAI announced that it is deepening its ties with the US government through a partnership with the National Laboratories and expects to use AI to “supercharge” research across a wide range of fields to better serve the public.
“This is the beginning of a new era, where AI will advance science, strengthen national security, and support US government initiatives,” OpenAI said.
In other advancements, Cerebras Systems announced today it will host DeepSeek’s breakthrough R1 artificial intelligence model on U.S. servers, promising speeds up to 57 times faster than GPU-based solutions while keeping sensitive data within American borders. The move comes amid growing concerns about China’s rapid AI advancement and data privacy.
And, the US Copyright Office issued AI guidance this week that declared no laws need to be clarified when it comes to protecting authorship rights of humans producing AI-assisted works. “Questions of copyrightability and AI can be resolved pursuant to existing law, without the need for legislative change,” the Copyright Office said.
In videos, let’s bust some early myths about DeepSeek. In episode 40 of Mixture of Experts, join host Tim Hwang along with experts Aaron Baughman, Chris Hay and Kate Soule. Last week, we covered the release of DeepSeek-R1; now that the entire world is up to speed, let’s separate the facts from the hype. Next, what is model distillation and why does it matter for competition in AI?
Then, recorded at TEDAI Vienna, AI researcher Youssef Nader and digital archaeologist Julian Schilliger share how they used AI to virtually “unroll” and decode the Herculaneum scrolls, burnt and buried by the eruption of Mount Vesuvius nearly 2,000 years ago. Learn how AI could help decipher a range of artifacts, revealing clues about the mysteries and achievements of the ancient world. And, the native 1080p AI Video from Pika can create hyper-realistic animals. Jerrod Lew is back with another demo of Pika 2.1 generating animals with text-to-video prompts.
BIG Projects To Solve Pressing Issues In Science — Dr. Christopher Stubbs, Ph.D. — Professor of Physics and Astronomy, Harvard University.
Dr. Christopher Stubbs, Ph.D. is the Samuel C. Moncher Professor of Physics and Astronomy, and has recently served as the Dean of Science in the Faculty of Arts and Sciences, at Harvard University (https://astronomy.fas.harvard.edu/peo…
Dr. Stubbs is an experimental physicist working at the interface between particle physics, cosmology and gravitation. His interests include experimental tests of the foundations of gravitational physics, searches for dark matter, characterizing the dark energy, and observational cosmology.
Dr. Stubbs was a member of one of the two teams that first discovered dark energy by using supernovae to map out the history of cosmic expansion.
Dr. Stubbs is currently heavily engaged in the construction of the Large Synoptic Survey Telescope (LSST), for which he was the inaugural project scientist. He founded the APOLLO collaboration that is using lunar laser ranging and the Earth-Moon-Sun system to probe for novel gravitational effects that may result from physics beyond the standard model.
The world of AI is evolving at a breakneck pace with new models constantly being created. With so much rapid innovation, it is essential to have the flexibility to quickly adapt applications to the latest models. This is where Azure Container Apps serverless GPUs come in.
Azure Container Apps is a managed serverless container platform that enables you to deploy and run containerized applications while reducing infrastructure management and saving costs.
With serverless GPU support, you get the flexibility to bring any containerized workload, including new language models, and deploy them to a platform that automatically scales with your customer demand. In addition, you get optimized cold start, per-second billing and reduced operational overhead to allow you to focus on the core components of your applications when using GPUs. All the while, you can run your AI applications alongside your non-AI apps on the same platform, within the same environment, which shares networking, observability, and security capabilities.


In today’s AI news, Block announced the launch of Goose, an open-source AI agent that allows developers to customize the tool for different purposes and using different large language models. Block’s move comes just after the Chinese startup DeepSeek unveiled its R1 artificial intelligence model, a rival to leading U.S. AI providers.
In other advancements, Cerebras and the Mayo Clinic, announcing a joint project for AI tools used in patient care. The technology was announced at the JP Morgan Healthcare Conference. In this project, the stakeholders aim to use a human reference genome to combine with patient data in order to try to identify genetic differences.
S innovative R1 reasoning model into its platform to revolutionize AI-powered search. This strategic integration strengthens Perplexity’s ability to perform deep web searches, providing users with more comprehensive and accurate results while upholding strict data security standards. + And, San Francisco-based start-up Atomicwork will today announce it has clinched $25 million of Series A financing in a round led by Khosla Ventures and Z47. The funding announcement comes less than six months after the last round, takes the total amount of money raised by the company since its launch to almost $40 million.
In videos, on this episode of Top of Mind, Gartner Global Chief of Research Chris Howard is joined by Rita Sallam, Distinguished VP Analyst, to explore how organizations can create measurable value with AI in 2025. Learn how to align investments with business priorities, manage productivity challenges and balance risk with ambition.
Ll gain a deeper knowledge of what makes a chatbot truly effective. + And, AI is transforming science in ways we never imagined. Bonnie Kruft, Deputy Director of AI for Science at Microsoft Research, shares how cutting-edge AI models are revolutionizing drug discovery, materials science, and climate prediction. Bonnie reveals how these innovations are shaping a healthier, more sustainable future for all.
S open-source model allows sharing of information, helping to lift all AI progress. He joins Caroline Hyde and Mike Shepard on “Bloomberg Technology” to discuss. ‘ + Thats all for today, but AI is moving fast — like, comment, and subscribe for more AI news! Please vote for me in the Entrepreneur of Impact Competition today! Thank you for supporting my partners and I, it’s how I keep Neural News Network free.
[](https://open.substack.com/pub/remunerationlabs/p/block-launc…hare=true)
A team of security researchers has disclosed new side-channel vulnerabilities in modern Apple processors that could steal sensitive information from web browsers.
The Georgia Institute of Technology and Ruhr University Bochum researchers, who presented another attack dubbed ‘iLeakage’ in October 2023, presented their new findings in two separate papers, namely FLOP and SLAP, which show distinct flaws and ways to exploit them.
The flaws stem from faulty speculative execution implementation, the underlying cause of notorious attacks like Spectre and Meltdown.
SEALSQ’s hardware solution highlights its post-quantum cryptography capabilities and adherence to global security standards.

Link :
Rare minerals discovered in Japan could be a game changer for their economic security.
A group of researchers in Japan uncovered a cache of rare minerals in the seabed around Minami-Tori-shima island harbours.
The Nippon Foundation and the University of Tokyo conducted a survey which discovered around 610,000 metric tons of cobalt and 740,000 metric tons of nickel.