FSO communication systems are where free space acts as a communication channel between transceivers that are line-of-sight (LOS) for successful transmission of optical signals. The channel can be atmosphere, space, or vacuum, whose characteristics determine the transmission and reception of optical signals for designing reliable and efficient communication systems. Using FSO technology data is transmitted by propagation of light through atmospheric or space communication channels, allowing optical connectivity. FSO communication offers a high data rate to meet the tremendous increasing demand of broadband traffic mostly driven by Internet access and HDTV broadcasting services. Compared to fiber optics technology, FSO offers much more flexibility in designing optical network architectures at very high speeds, at tens and hundreds of Gbit/s rates. However, FSO communication is affected by atmospheric effects, which limits sensitivity and achievable data rates with acceptable BER. Some of these degradations are turbulence, absorption, and scattering, and various mitigation techniques exist for reliable and efficient data transmission [1] and to increase the communication performance. Both point-to-point, point-to-multipoint, multipoint-to-point, and multipoint-to-multipoint FSO communications are possible, depending on the different scenarios of establishing optical links. FSO communication is the most practical alternative to solve the bottleneck broadband connectivity problem. The data rates provided by FSO links continue to increase in both long-and short-range applications. FSO will be one of the most unique and powerful tools to address connectivity bottlenecks that have been created in high-speed networks during the past decade due to the tremendous success and continued acceptance of the Internet. The next generation of Internet connectivity will push the limits of existing infrastructure with high-bandwidth applications such as videoconferencing, streaming multimedia content, and network-enabled portable devices. Clearing these bottlenecks is crucial for the future growth and success of the contemporary Internet society. The bandwidth of optical communications access and edge networks will be needed to satisfy these demands. Communication systems are concerned with the transmission of information from a source to a user. The purpose of a communication system is therefore to transfer information. A very basic block diagram of any communication system (optical or radiofrequency (RF)) is shown in Fig. 4.1.
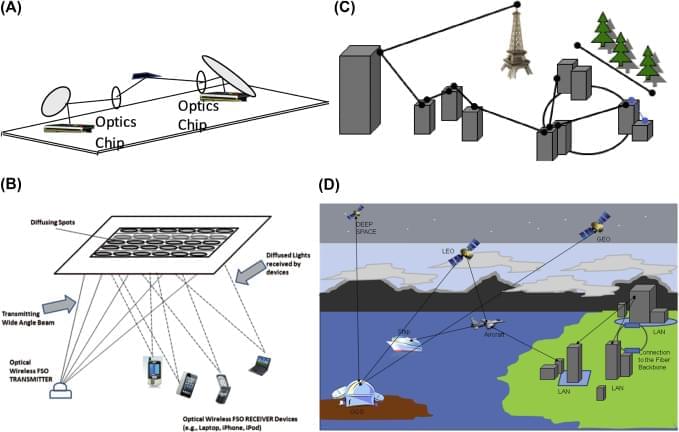
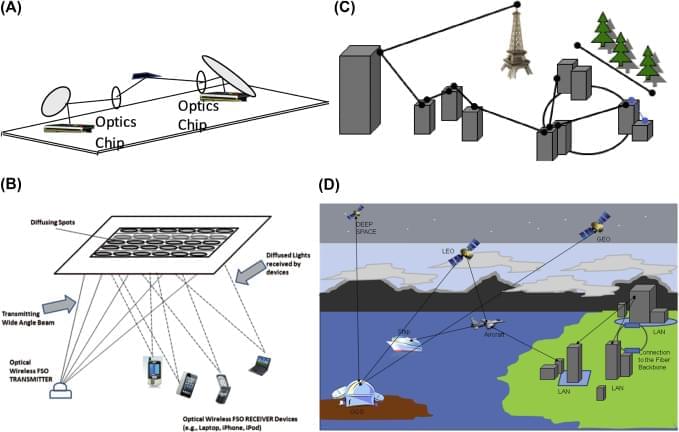
Fig. 4.1 shows a single point-to-point system, whereas in a multiplexed system there may be multiple input and output message sources and users (also called destinations). Fig. 4.2 shows other possible configurations and links for multipoint connections.
OWC is the next frontier for high-speed broadband connection and offers the following unique features and advantages: high bandwidth/capacity, ease of deployment, compact size, low power, and improved channel security. OWC can transmit and exchange voice and video communication data through the atmosphere/free-space at the rates of tens of Gbit/s and much more.