Aug 21, 2024
Computer scientists discover vulnerabilities in a popular security protocol
Posted by Saúl Morales Rodriguéz in categories: computing, internet, security
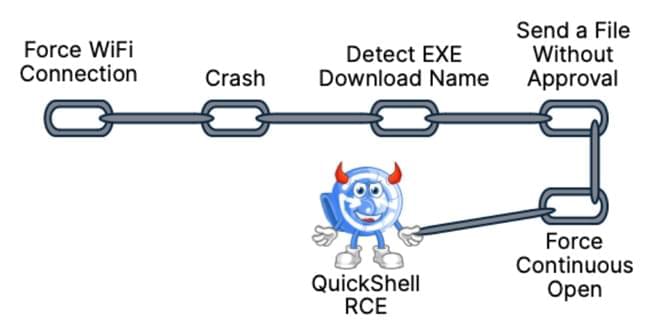
A widely used security protocol that dates back to the days of dial-up internet has vulnerabilities that could expose large numbers of networked devices to an attack and allow an attacker to gain control of traffic on an organization’s network.
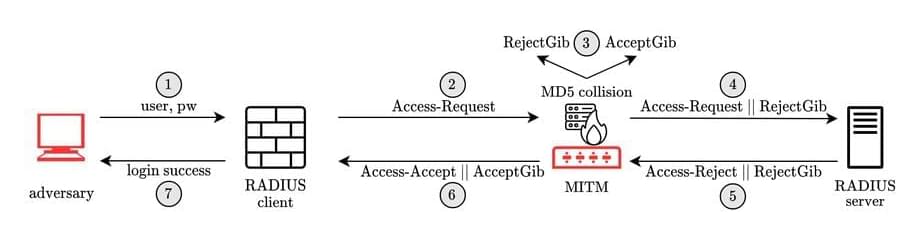
A research team led by University of California San Diego computer scientists investigated the Remote Authentication Dial-In User Service (RADIUS) protocol and found a vulnerability they call Blast-RADIUS that has been present for decades. RADIUS, designed in 1991, allows networked devices such as routers, switches or mobile roaming gear to use a remote server to validate login or other credentials.
This is a common set-up in enterprise and telecommunications networks because it allows credentials to be centrally managed. As a result, RADIUS is a critical part of modern telecommunications and enterprise networks; in large enterprises, it may control access to tens of thousands of switches.