Apr 15, 2021
Thousands of devices infected with the SolarMarket Trojan via malicious websites
Posted by Saúl Morales Rodriguéz in category: cybercrime/malcode
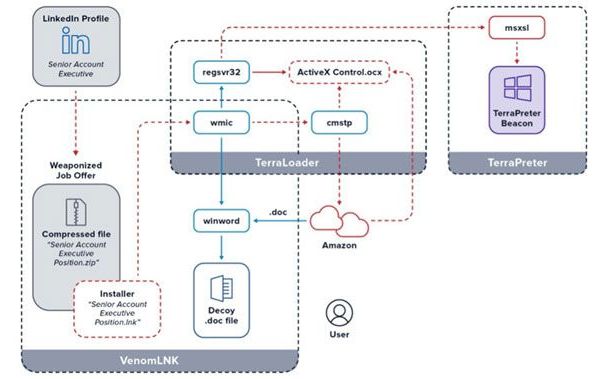
A recent report notes that a hacking group is employing search engine optimization (SEO) tactics to trick users into attracting them to over 100000 legitimate-looking malicious websites through the Google browser.
The goal of this campaign is to install a Remote Access Trojan (RAT) on vulnerable devices, which would allow the deployment of subsequent attacks and infections. The eSentire signature experts detected this campaign, mentioning that malicious web pages appear in browser results when the user searches for terms related to invoices, receipts, questionnaires and resume.