Sep 23, 2023
Free Download Manager releases script to check for Linux malware
Posted by Saúl Morales Rodriguéz in category: cybercrime/malcode
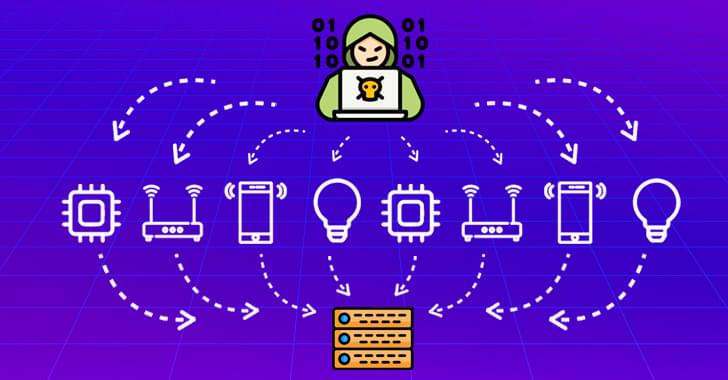
The developers of Free Download Manager (FDM) have published a script to check if a Linux device was infected through a recently reported supply chain attack.
Free Download Manager is a popular cross-platform download manager that offers torrenting, proxying, and online video downloads through a user-friendly interface.
Last week, Kaspersky revealed that the project’s website was compromised at some point in 2020, redirecting a portion of Linux users who attempted to download the software to a malicious site.

 עברית (Hebrew)
עברית (Hebrew)